Two-Hour Solution
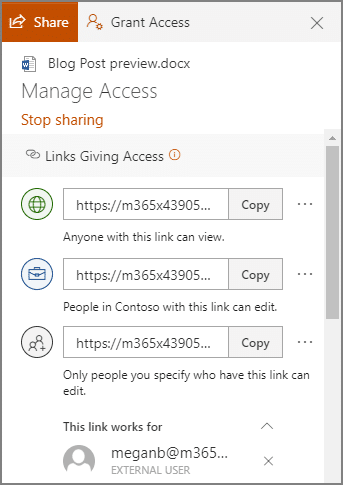
Roger Seip, author of Train Your Brain for Success, took a proactive and prepared look at productivity by developing his Two-Hour Solution. The idea is to take two hours to plan out a schedule to follow each week, based on how your plans and goals culminated the week before. Investing this time should allow you to make the most of your available time to accomplish what you want to accomplish.
The reason that this is different than simply going over your calendar each week is the fact that, if guided by the Two-Hour Solution, you’re figuring out how the time you’re spending contributes to your goals. “Green time” is time that helps you generate financial capital, while your “red time” is the time that you spend preparing for green time, without generating any profit. To account for the wrench in the works that would ordinarily throw off your schedule, you also include “flex time” to provide a buffer. What’s left is your “re-creation” time, where you recover from your productive endeavors by doing the things you want to do.
Prioritizing
Steven Covey is an educator and a businessman who came up with a philosophy to living a full life that can also apply to life in the office.
Consider your big priorities, your more flexible responsibilities, and your rote tasks in the workplace as large rocks, smaller stones, and sand, respectively. Your time is a bucket, ready to be filled with these items as you see fit.
Let’s say you decide to start with the “sand,” before trying to cram in the “rocks” and “stones.” Chances are pretty good that you won’t be able to accomplish very much at all, at least nothing of any circumstance. However, if you prioritize the more impactful rocks, then the stones, and fill in the rest of the space with your sand, your bucket—or workday—is then used as productively as possible, and anything you didn’t get to complete isn’t of consequence.
Two-Minute Rule
While there are countless variables that can potentially influence the amount of time a task will take to complete, you eventually get a feeling for the typical duration, right? So, some tasks can predictably take a significant amount of time, while others take almost no time at all to make it through. The idea of the Two-Minute Rule, thought up by productivity consultant David Allen, takes advantage of that difference. His strategy: if a task will take two minutes or less, do it.
If that seems too simple, it kind of is. The philosophy behind the Two-Minute Rule is to build up your motivation to tackle the larger responsibilities by successfully completing smaller tasks. Think about it—every task, regardless of how large it is, can be broken into smaller, more manageable chunks, chunks that can take mere minutes to complete. Once you’ve completed enough of these two-minute tasks, it only makes sense to see the greater responsibility through… and with the progress you’ve already made supporting you, completing it seems that much more feasable.
The Blastoff Method
Entrepreneur and motivational speaker Mel Robbins devised this practice to help overcome the mental blocks that encourage us to procrastinate rather than doing things that are good for us. Robbins posits that, by hesitating, we put the brain into “protection” mode—by thinking about everything that needs to be done between point A and point B, your brain ultimately prevents you from doing what you need to do. However, if that hesitation can be avoided, your productivity (or, by Robbins’ original theory, your well-being) will see benefits.
Her solution is to close the gap that hesitation creates between your capability to do a task and your perception of that task. Her recommendation is to, quite literally, treat yourself like a rocket and count down to your action. Focus on counting down…5,4,3,2,1… and act immediately, before your thoughts get in the way.
Scientifically, by doing so, you are bypassing a behavioral process and resetting an established habit loop… allowing better, more productive habits to be created instead. Give it a try next time you encounter a task you want to avoid starting.
Create a Time Crunch
We’ll wrap up with another method that Roger Seip came up with. If you really feel you work better on a deadline, add a bit of a hurdle as you are scheduling your “green time” … give yourself less time than you think you’ll need. The pressure can help you to focus. Naturally, you need to avoid any flex time you have assigned for this to work.
What methods do you use to keep yourself focused and productive? Do any of these approaches sound like something you want to try? Let us know in the comments!
For the technology solutions that can also help you improve your practical productivity, talk to us! Give us a call at (604) 513-9428 to discuss your options.